In this post, we will learn about memory management, what is memory management, memory management requirements in os, memory manager, memory management hardware in computer architecture, what is memory management in os, memory management hardware, storage management in operating system, memory management, memory protection, memory management in operating system pdf, what is memory management in operating system, what is memory management, memory management, etc....
Memory management requirements:
1. Relocation
2. Protection
3. Sharing
4. Logical Organization
5. Physical Organization
1. Relocation:
The programmer does not know where the program will be placed in memory when it is executed while the program is executing, it may be swapped to disk and returned to main memory at a different location (relocated). Memory references must be translated into the code to the actual physical memory addresses.
The address generated by the CPU is said to be a logical address. An address generated by MMU is called a physical address.
Physical address= Contents of Relocation register + logical address
2. Protection:
Processes should not be able to reference memory locations in another process without permission. It must be checked at run time. The memory protection requirement must be satisfied by the processor (hardware) rather than the operating system (software).
The word protection means provide security from unauthorized usage of memory. The operating can protect the memory with the help of base and limit register. Base registers consisting of the starting address of the next process. The limit specifies the boundary of that job, so the limit register is also said to be a fencing register.
3. Sharing:
Allow several processes to access the same portion of memory. It is better to allow each process access to the same copy of the program rather than have their own separate copy.
4. Logical organization:
Programs are written in modules. Modules can be written and compiled independently. Different degrees of protection given to modules (read-only, execute-only). Modules are shared among processes.
5. Physical organization:
Memory available for a program plus its data may be insufficient. Overlaying allows various modules to be assigned to the same region of memory.
Computer memory is organized into two levels:
Main memory and secondary memory. Main memory provides fast access at a relatively high cost and it is volatile that means it cannot provide permanent storage whereas secondary memory is slower and cheaper and it is a non-volatile object.
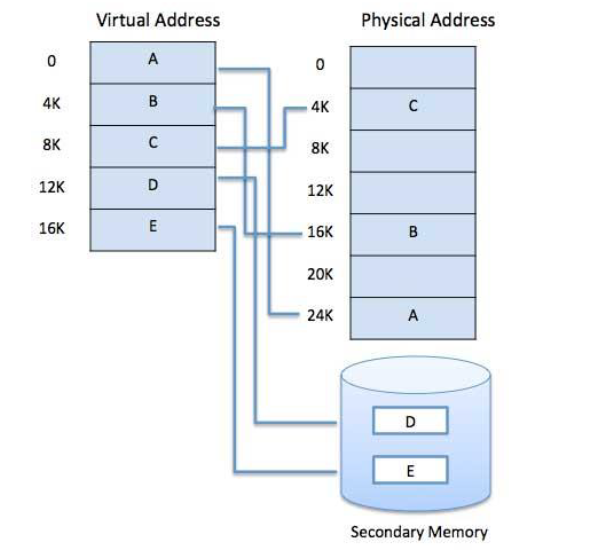
Virtual memory: A computer can address more memory than the amount physically installed on the system. This extra memory is actually called virtual memory and it is a section of a hard disk that's set up to emulate the computer's RAM.
The main visible advantage of this scheme is that programs can be larger than physical memory. Virtual memory serves two purposes. First, it allows us to extend the use of physical memory by using a disk. Second, it allows us to have memory protection because each virtual address is translated to a physical address.
Modern microprocessors intended for general-purpose use, a memory management unit, or MMU, is built into the hardware. The MMU's job is to translate virtual addresses into physical addresses. A basic example is given below −
Memory management requirements:
1. Relocation
2. Protection
3. Sharing
4. Logical Organization
5. Physical Organization
1. Relocation:
The programmer does not know where the program will be placed in memory when it is executed while the program is executing, it may be swapped to disk and returned to main memory at a different location (relocated). Memory references must be translated into the code to the actual physical memory addresses.
The address generated by the CPU is said to be a logical address. An address generated by MMU is called a physical address.
Physical address= Contents of Relocation register + logical address
2. Protection:
Processes should not be able to reference memory locations in another process without permission. It must be checked at run time. The memory protection requirement must be satisfied by the processor (hardware) rather than the operating system (software).
The word protection means provide security from unauthorized usage of memory. The operating can protect the memory with the help of base and limit register. Base registers consisting of the starting address of the next process. The limit specifies the boundary of that job, so the limit register is also said to be a fencing register.
3. Sharing:
Allow several processes to access the same portion of memory. It is better to allow each process access to the same copy of the program rather than have their own separate copy.
4. Logical organization:
Programs are written in modules. Modules can be written and compiled independently. Different degrees of protection given to modules (read-only, execute-only). Modules are shared among processes.
5. Physical organization:
Memory available for a program plus its data may be insufficient. Overlaying allows various modules to be assigned to the same region of memory.
Computer memory is organized into two levels:
Main memory and secondary memory. Main memory provides fast access at a relatively high cost and it is volatile that means it cannot provide permanent storage whereas secondary memory is slower and cheaper and it is a non-volatile object.
Virtual memory: A computer can address more memory than the amount physically installed on the system. This extra memory is actually called virtual memory and it is a section of a hard disk that's set up to emulate the computer's RAM.
The main visible advantage of this scheme is that programs can be larger than physical memory. Virtual memory serves two purposes. First, it allows us to extend the use of physical memory by using a disk. Second, it allows us to have memory protection because each virtual address is translated to a physical address.
Modern microprocessors intended for general-purpose use, a memory management unit, or MMU, is built into the hardware. The MMU's job is to translate virtual addresses into physical addresses. A basic example is given below −
Virtual memory is commonly implemented by demand paging. It can also be implemented in a segmentation system. Demand segmentation can also be used to provide virtual memory.
Demand Paging:
A demand paging system is quite similar to a paging system with swapping where processes reside in secondary memory and pages are loaded only on demand, not in advance. When a context switch occurs, the operating system does not copy any of the old program’s pages out to the disk or any of the new program’s pages into the main memory Instead, it just begins executing the new program after loading the first page and fetches that program’s pages as they are referenced.







1 Comments
2B4A0DE12D
ReplyDeletehacker kiralama
hacker arıyorum
tütün dünyası
hacker bul
hacker kiralama